- The Utah-based company that operates Canvas announced a deal Tuesday with hackers to delete swiped data.
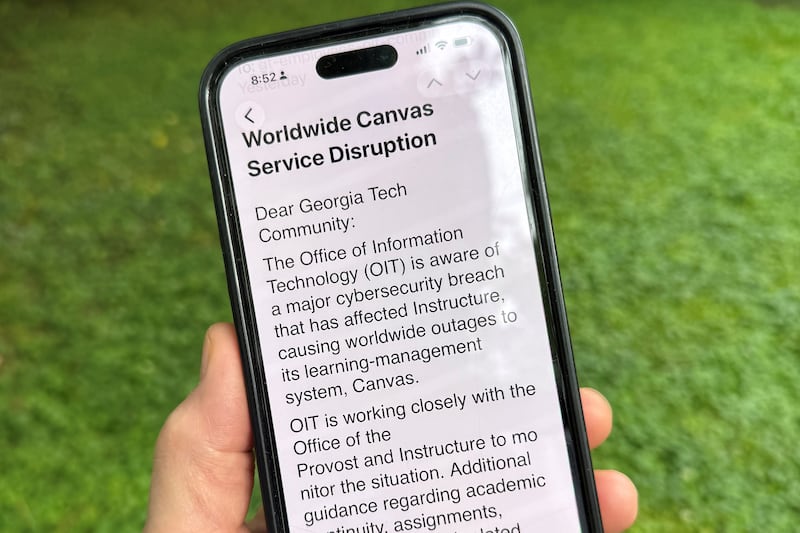
- The widely used online educational platform was targeted in a recent cyberattack.
- Congress has called for a briefing with Canvas company leaders to seek answers.
A deal has been reached between hackers and the Utah-based company that operates the Canvas online education platform following last week’s cyberattack that affected thousands of schools across the nation — including several in Utah.
Canvas’ parent company, Instructure, reported in an online post this week that it had reached “an agreement with the unauthorized actor involved in this incident.”
As part of that agreement, according to Instructure, the hackers returned all affected data while also digitally confirming that it had destroyed any remaining compromised data, in the form of “shred logs.”
The agreement covers all impacted Instructure customers, “and there is no need for individual customers to attempt to engage with the unauthorized actor.”
The educational technology company added that no Instructure customers will be extorted as a result of the recent cyberattack, “publicly or otherwise.”
Meanwhile, according to Instructure, Canvas is fully operational and safe to use. “We’ll give you clear guidance if any action is required on your end. Right now, there’s nothing you need to do.”
The Canvas system — which is used by students, parents and schools to manage grades, assignments, course notes and other digital tasks — was reportedly back online late last week.
The hacking group ShinyHunters claimed responsibility for the Canvas breach.
The cyberattackers reportedly posted online that nearly 9,000 schools worldwide were affected, with billions of private messages and other records accessed.
The data involved in the breach included information such as usernames, email addresses, course names, enrollment information and messages. “Core learning data” — such as course content, submission and credentials — was not compromised, according to Instructure.
“We continue to work with expert vendors to support our forensic analysis, further harden our environment, and conduct a comprehensive review of the data involved,” Instructure noted in its online post.
“As our investigation draws closer to a conclusion, we also intend to share additional details about the root cause and lessons learned, with the goal of helping the broader education technology community better understand and defend against similar threats.”
Congress seeking answers from Instructure
The company didn’t provide any details on the agreement, including whether it involved a payment, and didn’t confirm who was behind the hack. Instructure temporarily took the system offline while it investigated, locking out students and faculty, The Associated Press reported.
Even after news of the agreement between Instructure and the hackers, cybersecurity experts were skeptical the security incident was over.
Cynthia Kaiser, a former deputy director of the FBI’s Cyber Division, told The Associated Press that the reported deal suggests that a ransom was likely paid.
“What victims must understand is that payment does not end the threat,” Kaiser, now the senior vice president of the Halcyon Ransomware Research Center, said in a written statement. “Stolen data will be used against clients and users for as long as it remains profitable to do so.”
The recent cyberattack on Instructure has drawn the attention of Congress.
In a May 11, 2026, letter to Instructure CEO Steve Daly, Rep. Andrew Garbarino, R-N.Y., who chairs the Committee on Homeland Security, requested that Instructure CEO Steve Daly or a company senior representative brief the Congressional committee about the cyberattack in the coming days.
The letter referenced the two cyberattacks on Infrastructure in early May — and called for a “full and transparent accounting.”
“With students at more than 8,000 institutions navigating final examinations and end of semester deadlines, the disruption of a platform that Instructure itself describes as serving more than 30 million active users globally is a matter of national concern,” the letter noted.
The scale and timing of the Instructure breach, according to Garbarino, demonstrated “the inability of a major educational to contain a threat actor” following repeated intrusions.
“The briefing,” the letter noted, “should address the circumstances of both intrusions, the nature and volume of data accessed, the steps Instructure has taken and is taking to contain the threat and notify affected institutions, and the adequacy of the company’s coordination with federal law enforcement and the Cybersecurity and Infrastructure Security Agency (CISA).”
CISA serves as the nation’s lead civilian cybersecurity agency, playing a direct role in supporting organizations that have experienced “significant cyber incidents,” according to the letter.
An apology from Instructure
This week’s Instructure update on the recent cyberattack included an apology from Steve Daly, the company’s CEO:
“Over the past few days, many of you dealt with real disruption. Stress on your teams. Missed moments in the classroom. Questions you couldn’t get answered. You deserved more consistent communication from us, and we didn’t deliver it.
“I’m sorry for that.”
Daly wrote that Instructure made the call last week “to get the facts right” before speaking publicly about the cyberattack.
“That instinct isn’t wrong, but we got the balance wrong,” he wrote. “We focused on fact-finding and went quiet when you needed consistent updates. You’ve been clear about that, and it’s fair feedback. We will change that moving forward.”
Daly added that the company has launched a dedicated incident update page with breaking news as it evolves.